Kidd Keo on Twitter: "COLECCION “DRUGS & DRINKS” Disponible a partir de Mañana en https://t.co/TYUx5KTcrX, Entra en la pagina y echa un vistazo!! https://t.co/7Xl1tJvnMT" / Twitter

KEOCOUTURE on Twitter: "Keo Couture https://t.co/6ja4YjF3H3 @KiddKeo95Flames https://t.co/jRsRHIFTfg" / Twitter

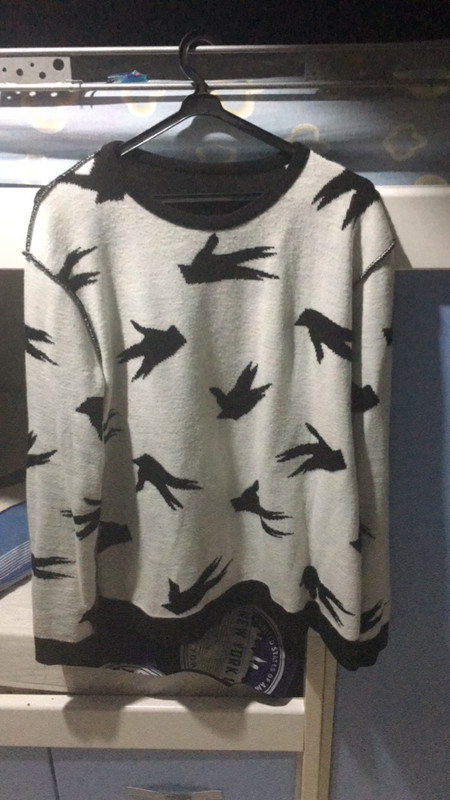
Kidd Keo Twitter પર: "SUDADERAS 24H ya Disponibles en https://t.co/i2f0FTeZr8 Limited 250 Las sudaderas vienen con sorpresa proximamente🙌🏻 Love you All💕 https://t.co/uWpNQUQcfW" / Twitter